Secure Payment Processing Solutions for Telehealth Businesses

Director of Cloud and Cybersecurity, AWS Expert, big fan of SRE. Helps teams to improve system reliability, optimise testing efforts, speed up release cycles & build confidence in product quality.
Today’s healthcare practitioners understand that the time is right to embrace the latest technology and do away with inefficient and paper-intensive systems.
According to Accenture, over 80% of healthcare executives have confirmed that the pace of digital transformation in their organization is accelerating, with 93% reporting a sense of urgency to condense a decade-long modernization drive into a couple of years.
In this article, we will study the actions that practitioners are taking to implement HIPAA-compliant payment processing. Plus, we will discuss what they need to do to stay on top of the ever-changing requirements, maintain patient trust and avoid hefty fines.
How Important Is Security in Healthcare Payment Processing?
Payment processing is a complicated component of any industry, but for healthcare professionals, it is especially sensitive. In a highly regulated sector where patients expect to be protected both personally and medically, confidentiality is a strong priority. There is also the ever-present fraud risk.
According to the 2022 AFP Payments Fraud & Control Survey, payment fraud is at record highs, with 71% of organizations registering incidents in 2021.
Practitioners must select a system that ensures the protection of payments as well as the personal data shared through these transactions. One of the most obvious challenges faced by medical practices is the task of ensuring HIPAA compliance.
HIPAA covers Protected Health Information (PHI), which refers to all of the information used to identify patients (from their name and credit card number to their date of birth, insurance information, and much more). This information is created, applied, or disclosed all the time as part of the process of healthcare delivery, including diagnoses and treatments.
The implications of failing to safeguard this data are serious. When healthcare staff are found to break HIPAA rules, they can be dismissed, sanctioned by the board, or even criminally charged and imprisoned. The minimum fine for willful HIPAA violation by an individual is $50,000; the maximum penalty is $250,000.
What are the Security Solutions for Payment Processing?
A majority of credit cardholders have confirmed that they have paid for medical costs with their card at some point. The most common credit card processing types in telemedicine are by phone, integrated software, and direct payment.
Regardless of the payment system, it is vital that healthcare providers take extra care to protect PHI; after all, manual processes that are vulnerable to human error can jeopardize your organization’s reputation.
Automated payment system
One possible solution is an automated payment system that has built-in fraud protection technology, including data and payment encryption capabilities. This helps to secure your practice’s financial records from external threats and preserves supplier relationships.
If you’re planning to introduce an AP system, HIPAA compliance should be at the forefront of your mind, as you need to ensure that any PHI included on an invoice is adequately safeguarded and protected.
Direct payment
If you decide not to go with an automated payment system, you need to be aware of several procedures or systems that you will need to adapt to stay HIPAA compliant when processing credit card payments.
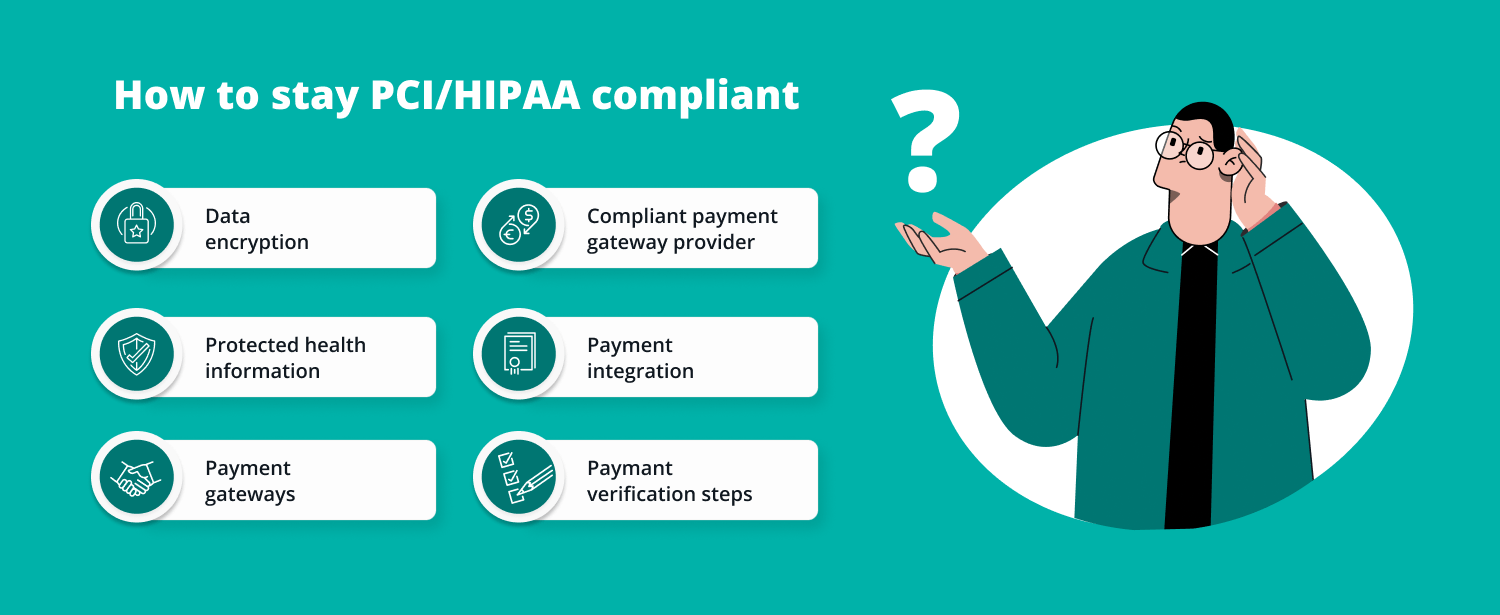
These include the following:
- Not giving any PHI, including data on treatment or care, when processing a patient’s card — just providing the bare minimum required for the payment to go through
- Avoiding issuing any receipts by text message or non-secure email — and ensuring that your processor doesn’t communicate using those methods, either
- Applying up-to-date encryption technology for payment data security, including point-to-point encryption and PCI-validated point-to-point encryption (vP2PE)
- Making sure any sensitive, unencrypted payment card data isn’t stored by electronic means or using any other system
- Replacing magnetic card readers with Mastercard, Visa, or Europay (EMV) chip card technology, which can lower the risk of counterfeit fraud by over three quarters
These actions will go a long way to ensuring that your patient’s PHI and credit card transactions are safe, secure, and kept well out of reach of the cybercriminals.
Now, let’s take a closer look at the specific technologies that make the task of HIPAA compliance and other regulatory commitments a lot easier for healthcare providers.
3D Secure (3DS) Card Authentication
3D Secure (3DS) is a security protocol that is used for the purpose of authenticating users. The objective is to enforce an additional layer of protection for payment card transactions in the card-not-present (CNP) context, which helps to prevent payment fraud, thwart unauthorized transactions, and minimize chargebacks.
If you maintain an eCommerce presence in the European Union (EU), you will probably be using 3DS. That’s because the EU’s Revised Directive on Payment Services (PSD2) necessitates the use of multifactor authentication (MFA) to complete a CNP transaction.
3DS has been adopted by:
- Visa,
- Mastercard,
- American Express,
- JCB,
- UnionPay,
- and Discover.
With the latest version, 3DS2, which was introduced in 2018, merchants need to provide authentication data together with payment card information. This process takes place unseen to the user and quickly authenticates the payment — unless the issuer detects any cause to suspect the legitimacy of the transaction.
If the transaction is flagged, users now receive a text message or confirmation code (using an app) to verify their identity — instead of being redirected to the bank’s website to confirm the password, as with the older version.
Today’s experience is much less disruptive for the user, with Visa reporting immediate approval for 95% of transactions and 40% less fraud.
SSL for Secure Connections
SSL (Secure Sockets Layer) is a protective measure to ensure patient privacy and safekeeping. Modern practices like to make use of web contact forms and comment sections (containing fields to enter names, telephone numbers and email addresses), which demands higher security standards, as HIPAA considers this text to fall into the category of PHI.
The answer is to protect any submitted form data with SSL technology, most likely by using SSL certificates. An integral part of the web today, these are tiny digital files that encrypt the communications (including sensitive data) between two computer applications on a network. That means all data traveling between your visitor’s browser and the website server.
Without the benefit of SSL, your patients' data is moving over public networks in clear text form – a breeze to capture, read and use with malicious intent by cybercriminals.
Email SSL certificates ensure end-to-end encryption to all outgoing emails. They validate the identity of the sender (binding it to a unique private key) and can be used to digitally sign business documents. In this way, certificates help healthcare companies comply with HIPAA’s section on technical safeguards.
The use of SSL has implications far beyond compliance. Google has been exploring ways to build a safer internet, and the search giant has indicated that SSL may play an influential role in search engine ranking decisions in future.
Card on File (CoF)
Business growth can make it difficult to stay on top of more complex inventory management tasks, increased customer communication, and even tackling the emergence of new rivals. This all means less time for teams to chase an expanding base of customers for overdue payments, while also maintaining their efforts to deliver the smoothest possible experience.
Fortunately, the practice of keeping customer credit cards on file has become an accepted part of the payment experience. Card on File (CoF) involves the merchant storing card information for repeat transactions, which ensures that future payments or subscriptions are settled in a timely and consistent fashion. ACH is the most common system for recurring expenses.
For the customer, CoF introduces the extra convenience of:
- one-click billing,
- wallet top ups,
- reauthorizations,
- frictionless checkouts,
- and much more.
The process demands much more of the merchant than just collecting credit card information, though. Under the terms of the Electronic Funds Transfer Act, merchants must gain their customers’ consent on the billing cycle related to the stored card. That usually means asking them to complete an online form or sign a receipt.
CoF sounds like a security risk, but due to the many high profile security breaches, there is now a strong aversion to storing primary account numbers (PANs). With today’s Europay-Visa-Mastercard (EMV) payment tokenization systems, the merchant is storing payment tokens in their database rather than the actual card number itself.
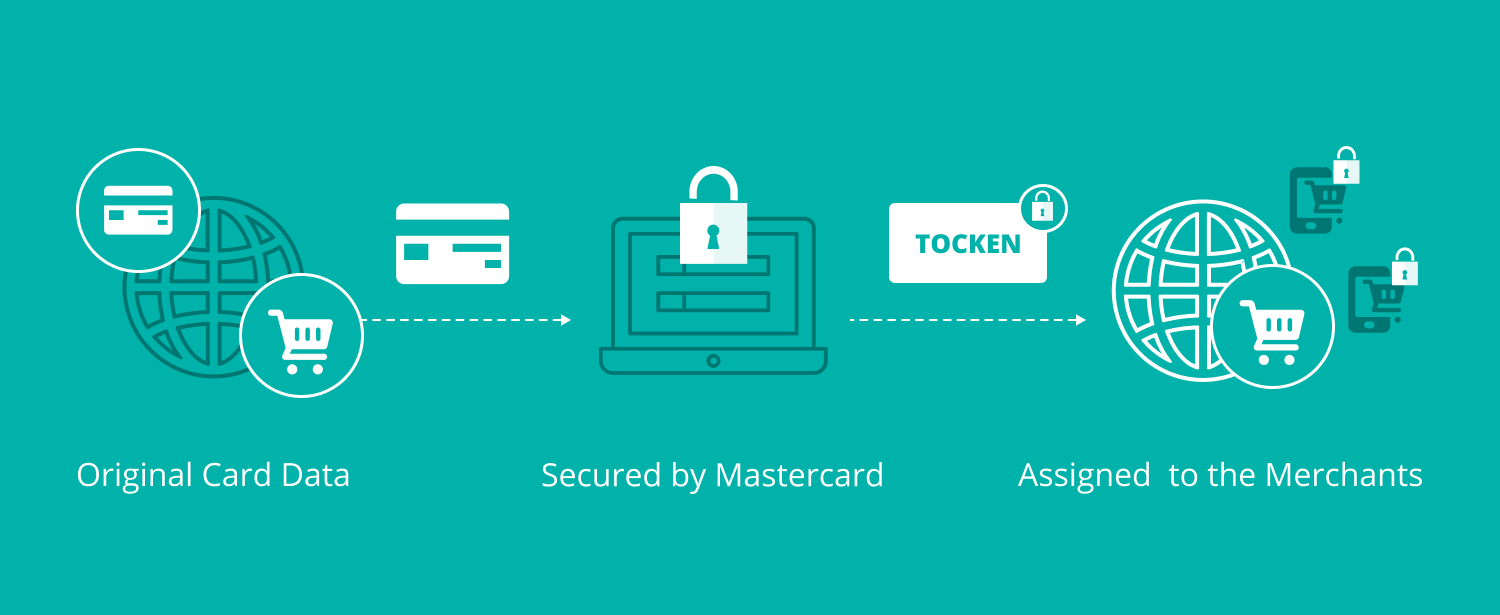
It’s a clever solution, and VISA, Mastercard and American Express continue to investigate ways of further advancing CoF methods. One recent innovation was an automatic update for stored payments in the event that a customer credit card is renewed or replaced. For the business owner, this helps to remove administrative hassle, and maintain cash flow.
Final Thoughts
We’ve covered just a few notable technologies here. A number of third party experts are able to help businesses with the challenge of automating payments, and optimizing digital invoicing and billing practices, while keeping in line with Payment Card Industry Data Security Standard (PCI DSS) compliance regulations.
When searching for partners, we suggest looking out for HITRUST Certification, which shows that a payment technology or solutions provider is not only PCI and HIPAA compliant, but also satisfies a number of other strict security standards including COBIT, ISO, and NIST.
An organization that is HITRUST Certified has demonstrated its adherence to best practices, and proven that it places security and data protection at the center of its business model.
With the effective application of technology and custom healthcare software development company, your customers’ private data should be as safe in the cloud as it is in their wallet. It can help you negotiate the increasing cost and sophistication of operating a healthcare practice, and gives you the tools you need to boost your bottom line.
Most importantly, a secure practice frees you up to concentrate on what you do best — taking care of your patients.
Are you keen to tighten up your security setup? Contact our team!



 Software Development
Software Development
 Security Services
Security Services
 Cloud Services
Cloud Services
 Other Services
Other Services
















 TechMagic Academy
TechMagic Academy
 linkedin
linkedin
 facebook
facebook
 twitter
twitter






















