Cloud Application Security Testing: 10 Best Practices
Last updated:2 March 2026

Keeping our data safe in the cloud is a big concern for companies, no matter their size. Protecting sensitive data, ensuring compliance, and safeguarding against malicious threats have become imperative tasks, especially in cloud environments where the traditional boundaries of networks are blurred.
But there's more to worry about with cloud security testing services. Cloud application security testing isn't just an additional layer of defense; it's a strategic imperative that ensures your organization's cloud infrastructure remains resilient against an ever-expanding array of cyber threats.
In this blog post, we will unravel the multifaceted dimensions of cloud security testing methodology, exploring best practices, innovative approaches, and techniques.
Key takeaways
- A secure cloud testing environment helps teams identify risks early and protect applications from data breaches, misconfigurations, and other security threats.
- Cloud app security testing is essential for detecting vulnerabilities across modern distributed systems and ensuring compliance with industry regulations.
- Effective testing requires continuous monitoring and analysis of cloud resources to maintain visibility and reduce security gaps across environments.
- A structured testing process, from vulnerability assessment to remediation and monitoring, helps organizations detect issues faster and respond to threats more effectively.
- Using the right testing tools allows teams to automate scans, run penetration tests, and integrate security checks into CI/CD pipelines.
- As businesses increasingly rely on cloud computing, proactive security testing becomes critical for protecting infrastructure, applications, and sensitive data.
What is Cloud Security Testing?
Cloud security testing is a type of security testing method in which cloud infrastructure is tested for security risks and loopholes that hackers can exploit. The main goal is to ensure the security measures are strong enough and find any weak spots that hackers could exploit.
This type of testing examines a cloud infrastructure provider’s security policies, controls, and procedures and then attempts to find vulnerabilities that could lead to data breaches or security issues. Cloud-based application security testing is often performed by third-party auditors working with a cloud infrastructure provider, but the cloud infrastructure provider can also perform it.
Security specialists perform security testing of cloud computing resources using a variety of manual and automated testing methodologies. The data generated by this testing type can be used as input for an audit or review. Not only this, but cloud security testing can also provide in-depth analysis and the risk posture of the security risks of cloud infrastructure.
Cloud cybersecurity testing becomes even more critical in multi-cloud security environments, where businesses use multiple cloud providers and need to ensure consistent protection across all platforms.

Cloud security testing is like the ultimate test to ensure your cloud setup is safe and aligns with what your organization needs. So, buckle up – by the end of this article, you'll be ready to master cloud security testing.
What are the advantages of cloud testing security?

- Compliance: The result is a harmonious blend of compliance and security, shielding your organization from penalties and unwelcome consequences. Achieving cloud security compliance ensures that your organization meets legal and regulatory requirements while maintaining high security standards.
- Financial кesilience: This proactive stance translates into substantial cost savings.
- Speed: The ideal cloud security testing should be adept at running parallel scans across multiple locations, drastically reducing the time needed to perform essential security checks.
- Scalability: Whether it's a bespoke in-house creation or a solution from a trusted vendor, scalability ensures that your testing capabilities keep pace with your ambitions.
- Quality: Crafting results that are not only accurate but also understandable.
- Minimizing кisks: Your cloud-based testing strategy should act as an impregnable shield, meticulously identifying, categorizing, and addressing potential risks.
Why Do You Need Cloud Security Testing?
Securing cloud environments isn't a mere extension of traditional security practices; it demands reimagining security strategies from the ground up. The nature of the cloud introduces complexities that require novel approaches.
In the conventional on-premises setup, security measures often revolve around the perimeter defense strategy, where robust firewalls and network security mechanisms guard against external threats. However, the lines between internal and external networks are blurred in the cloud. Virtualized resources, multi-tenant environments, and dynamic workloads challenge the very notion of a traditional perimeter.
Moreover, the cloud encourages a DevOps culture of rapid development, deployment, and continuous integration. While this approach fosters agility, it can inadvertently lead to security gaps if not vigilantly managed. The rapid pace of change in cloud environments necessitates security measures that are not just static but adaptive and responsive.
Why is all of this important? Well, picture this: the cloud is a bit like a busy city street. Lots of people are sharing the same space, and that can lead to new kinds of problems, like unlocked doors (misconfigurations), secret passageways (shared vulnerabilities), and intruders sneaking in (unauthorized access). As more and more folks move their digital stuff to the cloud, the city's getting busier, and the chances of something going wrong are rising.
And guess what? The bad guys aren't just twiddling their thumbs. They're getting smarter and developing new tricks to break into cloud systems. This is where cloud security testing comes to the rescue. It helps you find and fix the weak spots before those sneaky attackers can enter.
Here’s a quick reality check. In 2025, about 80% of companies reported experiencing a cloud security breach within the previous year, showing how common cloud-related incidents have become. At the same time, the financial impact keeps rising. The average cost of a data breach reached roughly $4.44 million globally in 2025, and incidents involving cloud environments can cost more than $5 million on average.
Check out these numbers:
- 65% of organizations say locating and fixing SaaS misconfigurations is still one of their biggest security challenges, according to the Cloud Security Alliance’s 2025 CISO survey.
- 25% of respondents said they experienced a SaaS security incident in the past two years, a much more defensible 2025 figure than the older “95%” claim.
- The global average cost of a data breach in 2025 is $4.44 million, and breaches involving public cloud environments average $5.17 million.
- 40% of breaches involve data spread across multiple environments, such as public cloud, private cloud, and on-prem systems, and those incidents take longer to contain and cost more than $5 million on average.

What Are the Main Threats Affecting Cloud Security?
- Insecure APIs: Weak APIs can expose sensitive data and create entry points for attackers. Without proper validation, authentication, and monitoring, they can lead to serious security vulnerabilities and large-scale breaches.
- Server misconfigurations: Mistakes in server setup, such as overly broad permissions, poor encryption settings, or weak separation of public and private data, can leave systems exposed. This is a common risk across modern cloud platforms.
- Outdated software: When updates are delayed or automatic patching is turned off, systems become easier to exploit. Regular maintenance and performance testing can help teams spot issues before they grow into bigger risks.
- Insecure coding: Poor coding practices can introduce flaws such as SQL injection, cross-site scripting (XSS), and cross-site request forgery (CSRF). Using reliable cloud testing tools helps teams identify these weaknesses earlier in development.
- Malware: Malicious software can steal data, interrupt services, and damage business operations. Running stress testing helps teams understand how systems behave under attack or heavy disruption.
- Data loss: Losing important business or customer data can lead to financial damage, legal issues, and loss of trust. Strong backup strategies and regular load testing help reduce the risk of service failure during critical moments.
- Insufficient identity and access management practices: Weak access controls make it easier for unauthorized users to reach sensitive systems. Using trusted cloud testing platforms can help teams review access flows, permissions, and related risks more effectively.
Effective Cloud Security Testing Checklist
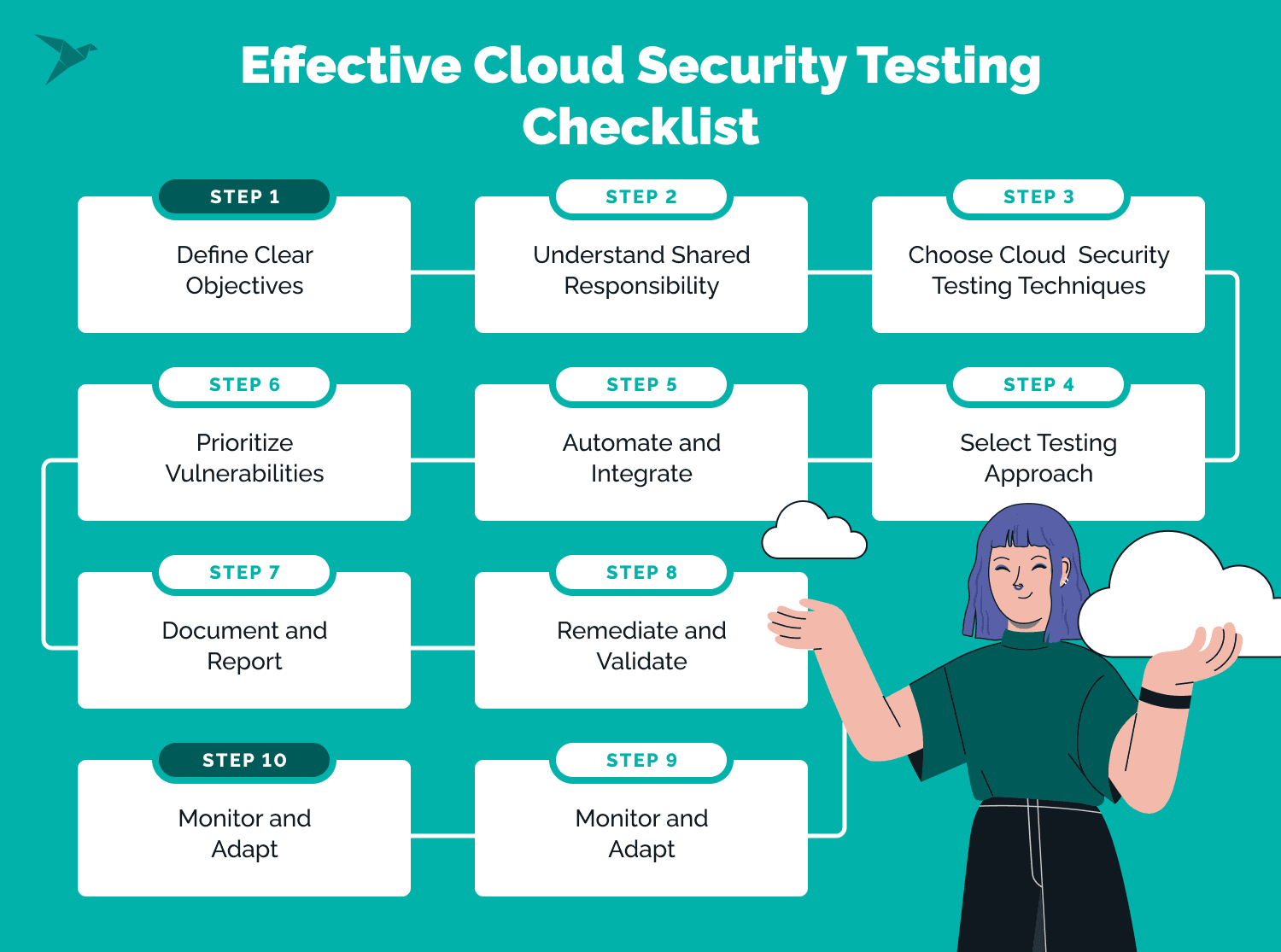 To ensure effective cloud security testing, follow this comprehensive checklist.
To ensure effective cloud security testing, follow this comprehensive checklist.
Step 1. Define clear objectives
Define a clear vision for your cloud security testing efforts. Establish specific security goals that align with your organization's overall security strategy. You can use existing security frameworks or standards like OWASP SAMM, AWS CIS, etc., to simplify the planning of mitigation measures implementation and progress tracking.
AWS cloud security best practices can enhance your testing by ensuring the security of the cloud infrastructure itself. Identify the scope of testing, including cloud assets, applications, and data to be evaluated. Set boundaries for the testing to ensure comprehensive coverage.
Step 2. Understand shared responsibility
Work closely with your cloud provider to understand the shared responsibility model and avoid security gaps. Define internal ownership for cloud security, since it involves testing controls regularly. Set clear oversight processes to support compliance and cloud testing scalability.
Step 3. Choose cloud security testing techniques
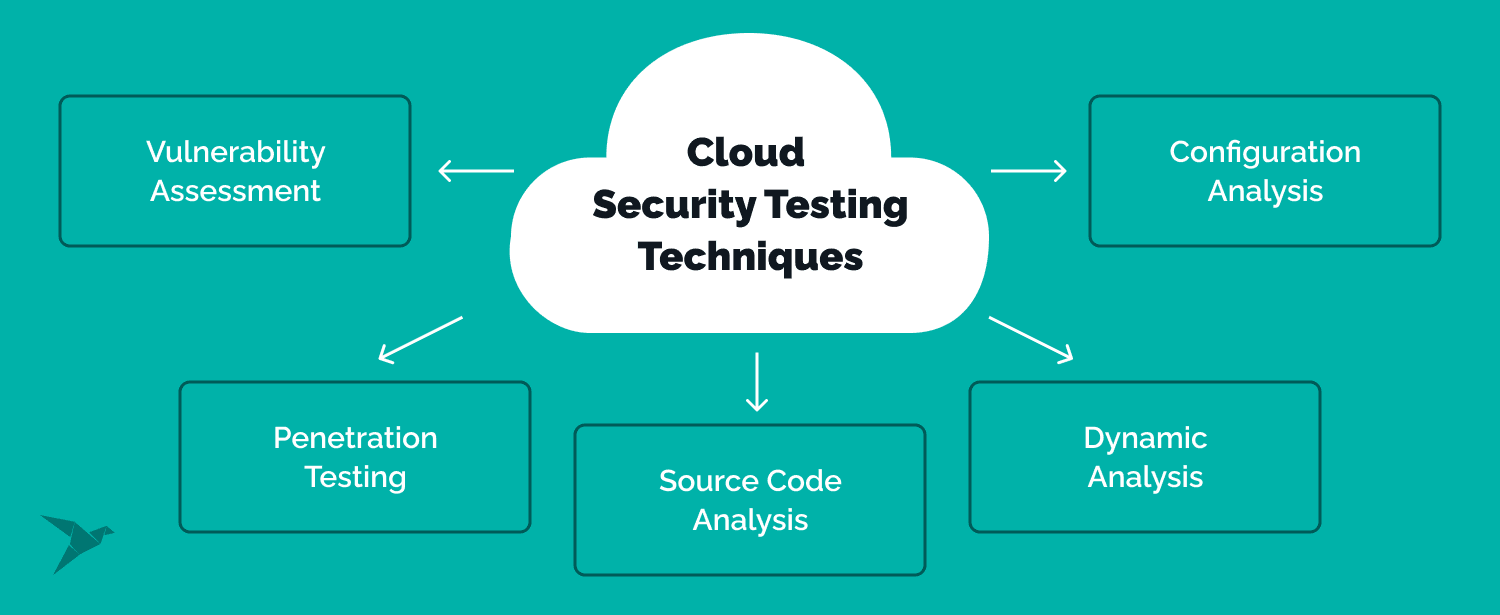
- Vulnerability Assessment: Vulnerability assessment: Use automated tools to find known weaknesses, misconfigurations, and exposed areas in your environment. This is a core part of testing in the cloud and helps teams fix issues before they turn into breaches.
- Cloud pen testing: Run controlled attacks to see how easily someone could break into your systems. This helps security teams validate defenses across different cloud platforms and uncover real attack paths.
- Source code analysis: Review application code to catch security flaws early, such as injection risks or weak input handling. It is especially useful for teams building on modern cloud computing services.
- Dynamic analysis: Monitor application behavior during runtime to detect issues that appear only in real use. This approach helps produce more accurate test results when systems are under normal or risky conditions.
- Configuration analysis: Check settings such as open ports, access rules, and encryption controls. This is particularly important in private cloud testing, where internal misconfigurations can still create serious security risks.
Step 4: Select testing approach
- Black Box Testing: Simulate real-world attacks without prior knowledge of the cloud environment. This approach tests the effectiveness of external security defenses and the organization's incident response. However, the limitations are apparent – testers lack contextual understanding and might miss intricate flaws.
- Gray Box Testing: Combine elements of both Black Box and White Box testing. Limited information about the cloud environment is provided, enabling testers to emulate insider threats. This approach marries the advantages of both black and white box testing. QA engineers possess sufficient insights to navigate the cloud landscape effectively while retaining an element of realism. Gray box testing excels when fine-tuning is crucial, especially in intricate setups where excessive access might disrupt normal operations.
- White Box Testing: Involves deep knowledge of the cloud infrastructure and applications. Testers can comprehensively assess security controls and uncover vulnerabilities. The advantage here is precision – testers can identify vulnerabilities with unparalleled accuracy. However, the limitation lies in its potential lack of real-world relevance, as security teams might approach challenges differently from hackers. White box testing thrives in scenarios demanding meticulous analysis, making it ideal for critical cloud systems where accuracy is paramount.
Step 5. Automate and integrate
Integrate automation tools for continuous security testing. Automate vulnerability scans, code analysis, and security checks to ensure consistent coverage and timely feedback. Embed security testing into your CI/CD pipelines to identify vulnerabilities early in development.
Step 6. Prioritize vulnerabilities
Rank issues based on risk, exploitability, and business impact. Consider how each weakness could affect your entire cloud infrastructure, especially in environments that include a hybrid cloud setup.
Step 7. Document and report
Record all findings, including vulnerabilities, misconfigurations, and possible attack paths. Give clear fixes and short summaries for stakeholders so testing teams can act faster and improve cost efficiency.
Step 8. Remediate and validate
Fix high-priority issues quickly, then retest to confirm they are fully resolved. This step is essential when testing software applications that run across shared and complex environments.
Step 9. Monitor and adapt
Use continuous monitoring, log analysis, and threat intelligence to detect new risks early. This is especially important as testing demands grow across cloud-based resources, data centers, and connected services.
Step 10. Continuous improvement
Review each test cycle, note lessons learned, and refine the process over time. Unlike traditional testing, cloud security testing must adapt constantly to changing threats, new deployments, and limits tied to physical hardware.
What Are the Types of Cloud Security Testing?
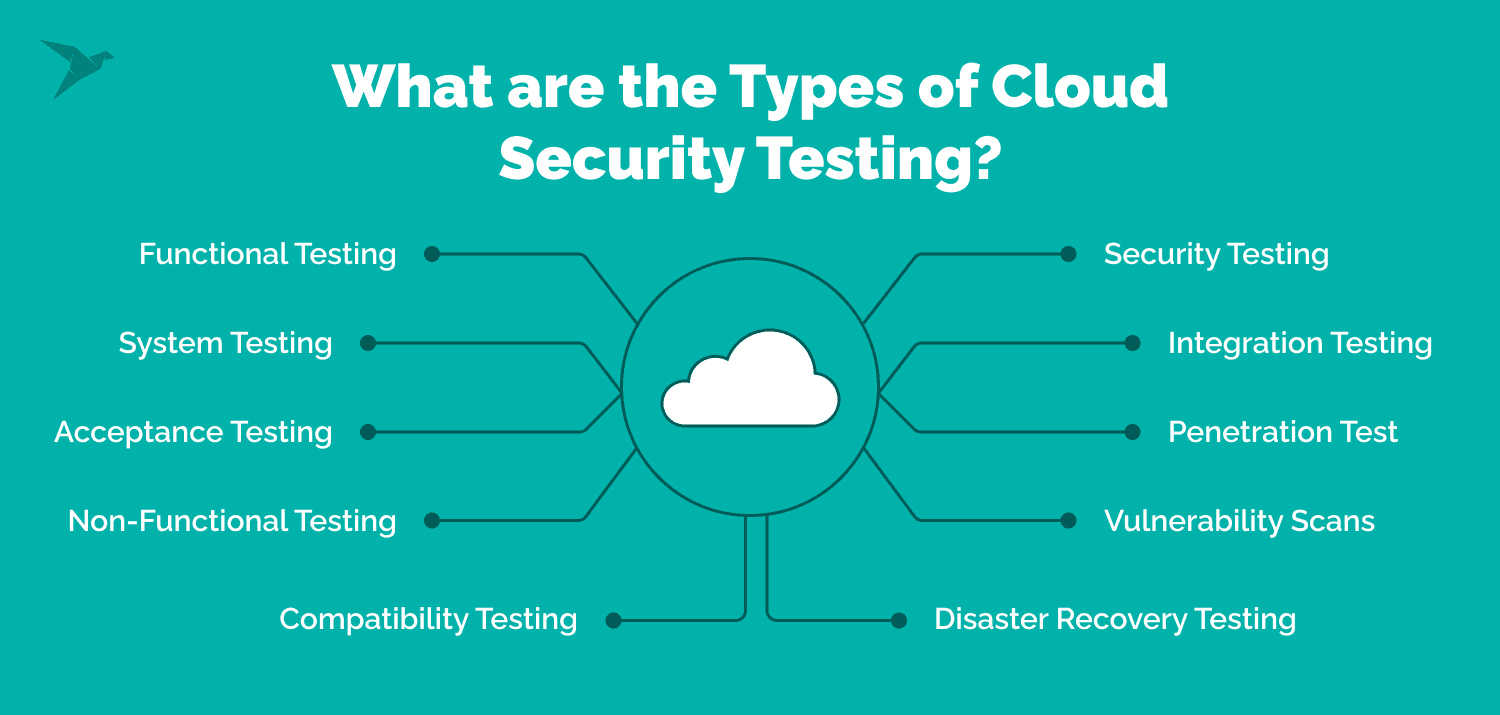
Functional testing
Functional testing verifies that each feature works as expected and meets user requirements. As part of software testing, teams run tests to confirm that every function delivers the intended result and supports a smooth user experience.
System testing
System testing evaluates how the entire application works as a complete system. It checks integrations, workflows, and supporting components within the overall testing infrastructure to ensure the solution operates correctly.
Acceptance testing
Acceptance testing confirms that the application meets business requirements and is ready for release. This step validates that the solution performs reliably before deployment to production environments.
Non-functional testing
Non-functional testing focuses on performance, reliability, usability, and response time. These are important benefits of cloud testing, especially when applications must support multiple users and maintain stable performance.
Compatibility testing
Compatibility testing ensures the application works across devices, browsers, operating systems, and environments. This is essential in multi-cloud testing, where systems rely on different cloud technologies, network configurations, and sometimes existing physical infrastructure.
Disaster recovery testing
Disaster recovery testing checks how well an application can recover after an outage, failure, or other disruption. It helps teams measure recovery time, reduce data loss, and keep cloud solutions available when problems occur.
Vulnerability scans
Vulnerability scans use automated tools to find known weaknesses in systems, applications, and configurations. This kind of continuous testing helps teams spot risks early and protect secure cloud-based applications more effectively.
Penetration testing
Penetration testing simulates real attack attempts to reveal weaknesses that automated scans may miss. It is an important part of app testing, especially when security is a significant challenge for complex systems.
Integration testing
Integration testing checks how different modules, services, and tools work together. It supports seamless integration across systems and helps teams confirm that connected components exchange data correctly.
Security testing
Security testing evaluates how well an application resists threats such as unauthorized access, data leaks, and misuse. It often includes scans, attack simulations, and web application-based tests to make sure cloud testing makes security validation part of the development process.
Best Practices for Implementing Cloud Security Testing from Our Experience
To fortify your digital stronghold, consider this comprehensive checklist that delves into the core tenets of cloud security:
Access management
Once security policies are defined, access management puts them into practice. It controls who can enter the system and what they can do. Common measures include role-based access, two-factor authentication, and secure VPN connections. These controls also help teams use testing resources more safely.
Backup and data recovery
Backup and data recovery protect systems when something goes wrong. They help restore lost data and return services to a stable state with minimal disruption. This is also a key part of availability testing, since recovery speed affects business continuity.
Regular penetration tests
Penetration tests help uncover weaknesses before attackers do. By simulating real intrusion attempts, they show where defenses need improvement and what should be fixed first. This approach works well with on demand testing when teams need fast validation after changes or updates.
Cloud-based firewalls
Cloud-based firewalls protect traffic, users, and workloads inside the cloud environment. Unlike traditional setups, they scale more easily and adapt to changing usage patterns. They are especially useful when working with a cloud service provider that supports dynamic infrastructure and distributed systems.
Learn how we helped Elements.Cloud set up cybersecurity for their product

Intrusion detection
Choose a cloud security tool with advanced intrusion detection capabilities. These systems use machine learning to monitor activity and identify unusual patterns in real time. When suspicious behavior appears, the system alerts security teams so they can respond quickly and prevent potential breaches.
Regular vulnerability checks
Frequent vulnerability assessments help detect weak points in your cloud environment before attackers do. Combine automated scans with manual reviews to uncover configuration issues and software flaws. These checks can also complement browser performance testing, ensuring applications remain both secure and stable for end users.
Strengthen your cloud security with TechMagic
A one-size-fits-all approach won't suffice; the uniqueness of cloud security threats mandates a tailored response. Cloud security testing is a linchpin in this response, offering a systematic method to identify vulnerabilities, assess risks, and fortify defenses.
Robust testing strategies need to account for the fluid nature of cloud architecture and the shared responsibility model between cloud providers and users. They should encompass various testing methodologies and techniques spanning reconnaissance, vulnerability assessment, penetration testing, and beyond. Only by embracing a holistic approach to cloud security testing can organizations uncover vulnerabilities, assess risks, and proactively protect their cloud-based assets.
TechMagic is more than security testing services provider; we're your partners in safeguarding your cloud ecosystem. With our expertise, your cloud security testing gains a new dimension—fortified, proactive, and geared towards ensuring your digital assets remain impenetrable.
Get in touch with TechMagic today and elevate your cloud security testing to new heights.

FAQ
Regular vulnerability assessments offer a proactive approach to identifying and addressing security weaknesses within your systems. By conducting these assessments, you gain insights into potential vulnerabilities before they can be exploited by malicious actors, enhancing your overall security posture.
Yes, we offer cloud penetration testing services. Our experts simulate real-world attacks on your cloud infrastructure to uncover vulnerabilities and provide actionable recommendations to fortify your defenses.
We provide various cloud testing services tailored to your needs, including comprehensive vulnerability assessments, penetration testing, data encryption, and access control analysis, and ongoing security monitoring. Our services are designed to address various aspects of cloud security, ensuring a holistic approach to safeguarding your digital assets.

















 TechMagic Academy
TechMagic Academy



