Cloud Security Compliance: What Security and Risk Leaders Need to Know
Last updated:3 April 2026
Most enterprises run across two or more cloud providers. Each new service speeds up delivery, and it also adds another set of identities, configurations, and audit trails to manage. For security and risk leaders, that growth brings a hard question: How to prove our controls work at any moment, not only during an audit?
Here, cloud security compliance becomes truly critical. Ownership is split under the shared responsibility model, multi-cloud architectures introduce inconsistent control surfaces, regulations continue to evolve. Evidence must be ready on demand, and aligning cloud security and compliance across different teams is no small task.
In our new article, you will learn what cloud security compliance really means in operational terms, why cloud environments make regulatory alignment more difficult than traditional infrastructure, and how to deal with it. We’ll also discuss which major regulations shape cloud control requirements, the most common compliance mistakes, and how to avoid them.
Key takeaways
- Cloud compliance requires continuous enforcement and validation, not periodic audit preparation. That is the foundation of a compliant cloud environment and stronger information security.
- The shared responsibility model must be mapped at the service level to prevent control gaps, especially in cloud-based systems where ownership is not always obvious.
- Multi-cloud environments increase identity, configuration, and evidence complexity, which can weaken your cloud security posture if teams do not apply robust security controls consistently.
- Regulatory requirements must be translated into specific technical safeguards, from security policies to robust security measures, and monitored against relevant data protection laws and data residency requirements.
- Strong alignment between legal, security, and engineering teams helps organizations protect sensitive operations like financial reporting and maintain customer trust while reducing risk and audit friction.
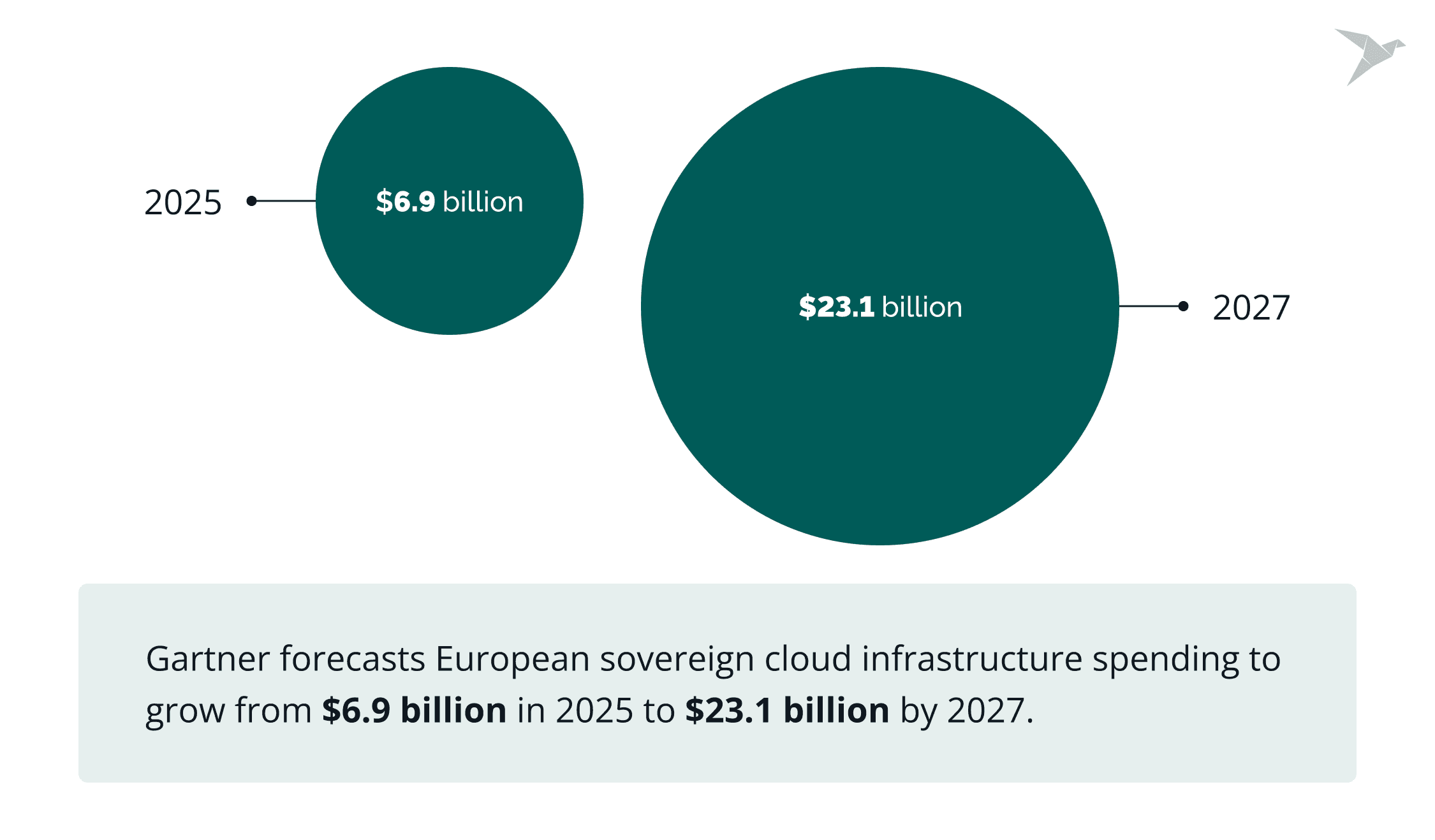
What Is Cloud Security Compliance?
Cloud security compliance means meeting legal and regulatory requirements while running systems and handling data in cloud environments. It comes down to turning obligations into controls you can enforce and prove.
By and large, it covers how you protect sensitive data stored in the cloud, apply strong access control measures, monitor activity, and manage risk in cloud services. It also covers how you document those controls so you can show they work.
At its core, cloud security compliance is about two things:
- Understanding what the law or standard requires.
- Proving that your cloud environment enforces it.
It sits at the intersection of governance and engineering. Legal and compliance teams interpret cloud security compliance standards such as CIS Benchmarks. Security and cloud teams implement identity controls, encryption, monitoring, logging, and policy enforcement as a part of cloud security strategy to meet those expectations.
Why the cloud makes compliance different
Cloud changes compliance because responsibility is shared, and configurations change constantly. A cloud provider can secure the underlying platform, but your organization still owns how identities are managed, how data is protected, how workloads are configured, and how evidence is captured. That is why such regulatory compliance is an ongoing operational discipline.

Why Is Cloud Security Compliance So Challenging?
Speaking generally, cloud security compliance is challenging because ownership is split, cloud footprints are spread across services and providers, and regulatory expectations keep changing. In practice, teams end up tracking the same control in multiple places, using different tooling, and producing audit evidence from fragmented logs and policies.
Multi-cloud adoption adds to the load. Over 78% of organizations now use two or more cloud providers , and multi-cloud environments were a key driver of security and compliance complexity in 2025.

Let’s take a closer look at these challenges.
The shared responsibility model divides security duties
The shared responsibility model splits security duties between the cloud provider and the customer. Providers typically handle the security of the cloud (facilities, hardware, core services). Customers handle security in the cloud (identity, access, configuration, workloads, and data).
What it leads to is that compliance issues show up when that split isn’t mapped service-by-service. A control that’s partly covered in one managed service can be fully on you in another. That creates gaps in policy enforcement, monitoring, and audit evidence (especially when multiple teams “own” different pieces of the stack).
Multiple cloud environments and service models have different control surfaces
IaaS, PaaS, and SaaS each come with different control surfaces. Add more than one cloud provider, and you’re dealing with different identity models, logging formats, encryption defaults, and configuration patterns.
That leads to common pain points:
- Inconsistent policy enforcement across platforms.
- Separate monitoring and alerting pipelines.
- Duplicated evidence collection for audits.
- Higher risk of configuration drift over time.
Recent incident research also keeps pointing back to preventable issues in identity and configuration. Palo Alto Networks Unit 42 reported that 90% of incidents involved identity weaknesses and called out widespread excessive permissions in cloud identities. So, multi-cloud security must be prepared.
Constantly evolving regulatory requirements
Compliance requirements shift as regulators react to new risks, new technologies, and high-profile incidents. Updates rarely land as “one small change”, and typically affect how you document controls, how you prove enforcement, and how you monitor exceptions.
This is why cloud computing security compliance often feels continuous. Policies and technical controls need frequent tuning, and audit-ready evidence has to stay current rather than being assembled at the last minute.
Data residency and cross-border data flows are difficult to manage
Data residency rules and cross-border transfer requirements add legal and architectural constraints. Even when workloads stay in-region, logs, backups, analytics pipelines, and support processes can move data across borders unless they are designed carefully.
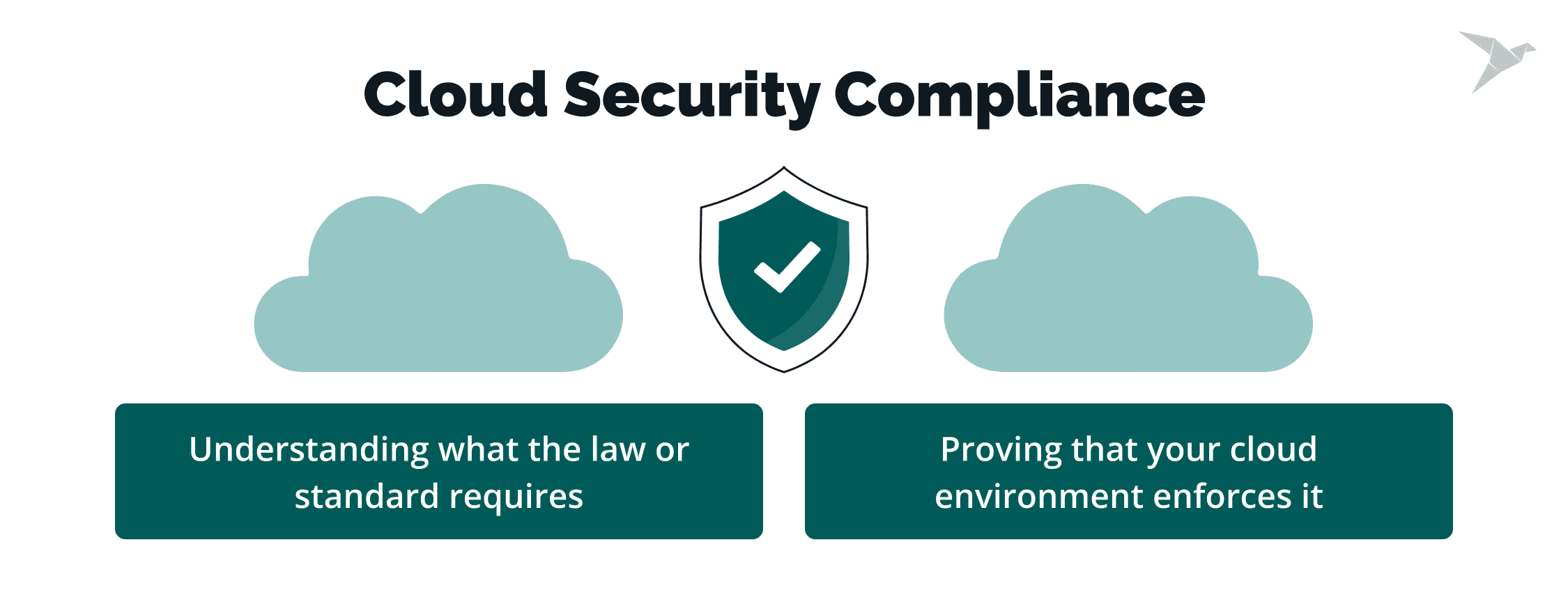
Sovereignty pressure is also rising. Gartner forecasts European sovereign cloud infrastructure spending to grow from $6.9 billion in 2025 to $23.1 billion by 2027, so there is a stronger demand for local processing and control.
Which Regulations Apply to Cloud Security Compliance?
There are several major regulations and frameworks that shape how organizations secure data in the cloud. The exact set depends on your industry, geography, and the type of data you process. In cloud environments, these rules translate into concrete technical safeguards, governance processes, and ongoing monitoring.
Center for Internet Security (CIS) Benchmarks
CIS Benchmarks are a set of best-practice guidelines for securely configuring systems, including cloud platforms like AWS, Azure, and Google Cloud. Unlike regulatory frameworks, they are not tied to a specific law but provide practical, technical guidance on how to harden cloud environments.
In the context of cloud security compliance, CIS Benchmarks help translate high-level requirements into concrete configurations. For example, they define how to set up identity and access management, logging, network controls, and secure defaults across cloud services.
Organizations often use CIS Benchmarks as a baseline to:
- identify misconfigurations early;
- standardize security settings across environments;
- support audit readiness with clear, repeatable controls.
They are especially useful in multi-cloud setups, where consistency is harder to maintain. By aligning configurations with CIS recommendations, teams reduce risk and make it easier to map technical controls to broader compliance frameworks like GDPR, HIPAA, or SOC 2.
In practice, CIS Benchmarks do not replace regulatory requirements. Instead, they act as a technical foundation that helps organizations implement and maintain secure configurations in a structured and measurable way.
General Data Protection Regulation (GDPR)
GDPR applies to organizations that process personal data of individuals in the European Union. In a cloud context, this affects how you store, transfer, access, and delete data.
Cloud deployments must support strong access control, encryption, logging, and clear data processing agreements with providers. Organizations also need visibility into where personal data resides and how cross-border transfers are handled. In practice, GDPR compliance in the cloud requires close coordination between legal, security, and cloud architecture teams.
Health Insurance Portability and Accountability Act (HIPAA)
HIPAA governs the protection of health information in the United States. When healthcare data is stored or processed in the cloud, organizations must ensure that administrative, technical, and physical safeguards are in place.
This includes:
- strict identity management;
- encryption in transit and at rest;
- detailed activity logging;
- formal agreements with cloud providers that define security obligations.
Cloud environments must also support auditability and incident response processes aligned with healthcare requirements.
Payment Card Industry Data Security Standard (PCI DSS)
PCI DSS applies to all organizations that handle payment card data. In the context of cloud environments, this requires clear scoping of where cardholder data exists and how it is segmented from other systems.
Technical controls typically include:
- network segmentation;
- vulnerability management;
- strong authentication;
- logging;
- continuous monitoring.
The organization and the cloud provider must clearly define responsibility, especially when using managed services.
System and Organization Controls (SOC 2)
SOC 2 is an attestation framework focused on security, availability, processing integrity, confidentiality, and privacy. It evaluates whether controls are properly designed and operating effectively over time.
In cloud environments, this means documenting policies, enforcing consistent access controls, maintaining change management processes, and generating reliable audit evidence from cloud systems. The emphasis is not only on having controls, but on proving they work consistently.
Federal Risk and Authorization Management Program (FedRAMP)
FedRAMP applies to cloud services used by U.S. federal agencies. It defines a standardized security assessment and authorization process for cloud providers and, in some cases, for organizations delivering services to government entities.
Cloud environments subject to FedRAMP must meet strict baseline controls, continuous monitoring requirements, and detailed documentation standards. The framework demands structured governance and disciplined configuration management across the cloud stack.
Each of these regulations applies differently depending on your business model and data flows. What they share is a common expectation: security controls must be clearly defined, technically enforced, continuously monitored, and backed by evidence. In cloud environments, meeting that expectation requires both regulatory understanding and disciplined cloud engineering.
How Are Cloud Technology Security Requirements Met?
In two words, to meet cloud technology security requirements, you need to have a clear understanding of your security risks, enforce proper controls, and prepare evidence for review. This is what makes a cloud security compliance strategy workable in real operations. Let’s discuss all the essential steps in more detail.
Risk assessments and gap analysis
The best practice is to start by mapping data, systems, identities, and third parties. Then you can assess risk and compare current controls to regulatory and contractual requirements. The output should be clear: what is missing, what is weak, what is out of scope, and what needs remediation first.
Security controls implementation (encryption, access management, etc.)
Here, the main task is to turn requirements into controls that are consistently applied across cloud services. This typically includes encryption, access management, secure configuration baselines, logging, and monitoring. The goal is enforceable controls. Many teams rely on cloud security services to standardize deployment and reduce drift across environments.
Regular audits and continuous compliance checks
Security is not a one-team effort. Both security and DevOps teams play a role in running scheduled control checks and continuous monitoring. DevOps teams, in particular, can set up and manage native or additional monitoring and auditing tools as part of everyday operations.
Cloud environments change constantly, so control validation needs to be frequent enough to catch permission creep, misconfigurations, and unmanaged assets early before they turn into audit findings.
Detailed documentation and evidence for audits
We always treat evidence as a system output. What it means is you need to collect logs, configuration snapshots, access reviews, change records, and incident documentation in a consistent format. Keep it traceable to specific controls so audits become review, not reconstruction.
What Are the Most Common Cloud Security Compliance Mistakes?
The most common mistakes come from false assumptions, weak control enforcement, and outdated practices. Cloud environments move fast. Compliance programs often don’t.
When organizations approach cloud computing with compliance and security as separate tracks, gaps appear quickly.
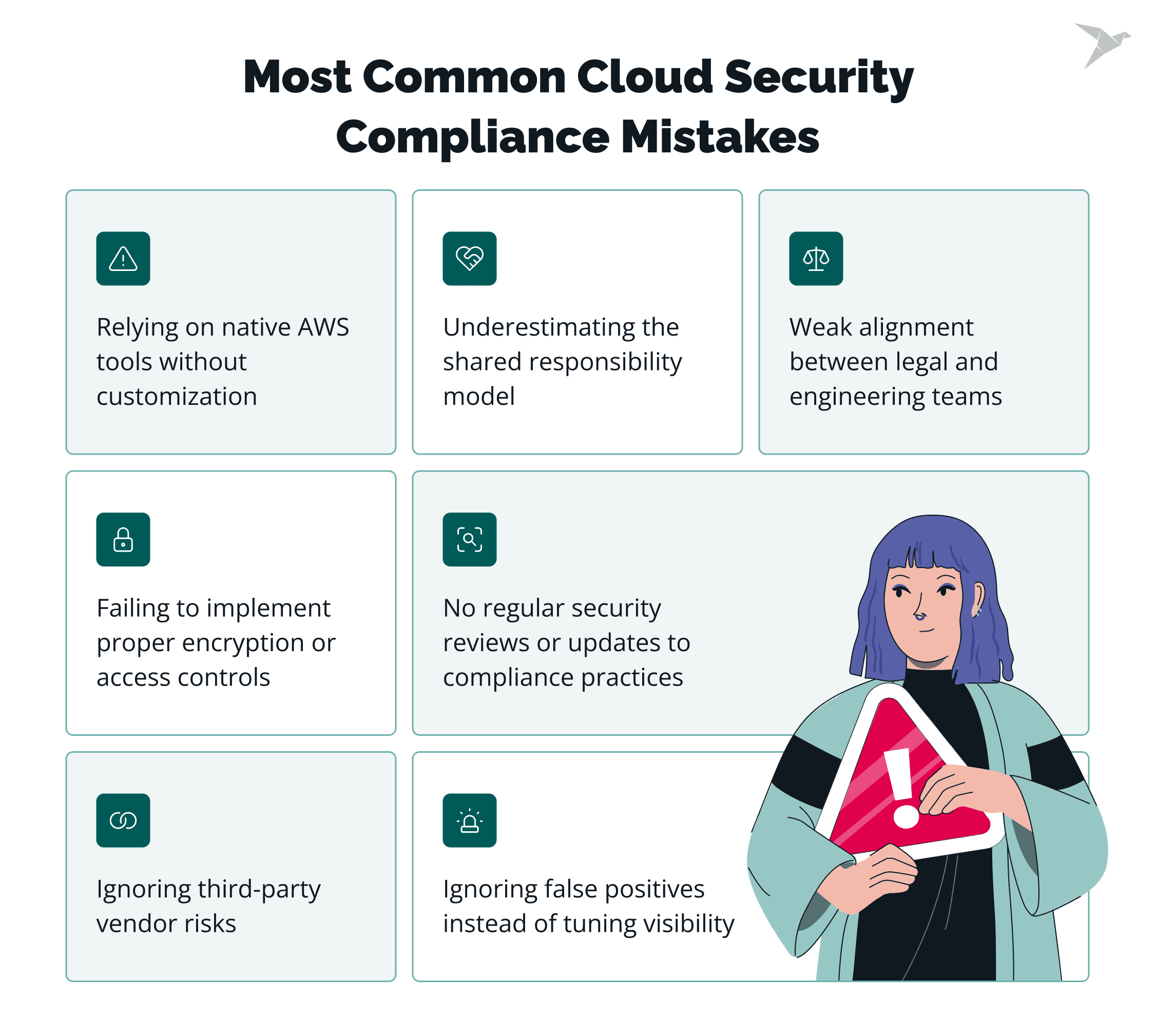
Relying on native AWS tools without customization
A common mistake is assuming native AWS tools will give you audit-ready evidence with little extra work. AWS includes many built-in capabilities, but they do not automatically fit your control environment, reporting needs, or internal workflows. Every environment is different, so without customization, these tools often create noise instead of useful evidence.
To make them effective, treat evidence as a system output. Collect logs, configuration snapshots, access reviews, change records, and incident documentation in a consistent format, and map them to specific controls. That is what turns audit preparation into a review process instead of a last-minute reconstruction exercise.
Underestimating the shared responsibility model
As we’ve said before, providers secure the infrastructure, and your task is to secure identities, configurations, workloads, and data. The mistake is not mapping responsibilities at the service level. For instance, in the case of AWS cloud security, control ownership can shift depending on whether you use managed services, containers, or virtual machines.
The general fix is to map responsibility per service, validate configurations regularly, and align control ownership across security and engineering teams.
Ignoring third-party vendor risks
Cloud environments rely on SaaS platforms, managed services, and integration partners. Each third party adds risk. A common mistake is reviewing vendors only during onboarding. After that, oversight weakens, certifications expire, controls change, and data flows expand.
To avoid this, treat vendor risk as ongoing. Review attestations regularly, monitor integrations, and ensure contracts define security obligations and reporting expectations.
Weak alignment between legal and engineering teams
Compliance language is often interpreted differently by legal and technical teams. Legal teams focus on obligations and wording, and engineering teams focus on implementation details and platform constraints. When those interpretations don’t meet in the middle, controls may look correct on paper but fail in practice.
The fix is shared control mapping. Translate regulatory requirements into specific cloud controls, agree on ownership, and document the “why: behind architecture decisions. This makes audits smoother and reduces rework during security reviews.
Failing to implement proper encryption or access controls
Encryption and access control appear in almost every compliance framework, yet misconfigurations remain common. Over-permissioned identities, shared credentials, inconsistent encryption policies, and incomplete logging create exposure. These gaps often surface during audits or incidents.
Least-privilege access, enforced encryption baselines, strong key management, and automated configuration checks reduce this risk.
No regular security reviews or updates to compliance practices
Compliance programs often start strong and then become static, but cloud environments do not. Your cloud provider can deploy new services, change architectures, and regulations evolve all the time. If policies and controls are not reviewed, they drift away from real system behavior.
Schedule regular reviews of risk assessments, access rights, logging coverage, and regulatory mappings. Continuous validation keeps compliance aligned with reality.
Ignoring false positives instead of tuning visibility
Another common mistake is relying on default visibility across multi-cloud environments without enough customization. In practice, teams often lack a unified view of assets, identities, and data flows across cloud providers, and that creates blind spots. On top of that, security teams may face a high volume of false positives that are not added to a mute list for a clear reason and are simply ignored over time.
That usually points to a deeper issue: limited tuning and an incomplete understanding of actual risk. Without customization, alerts become noise instead of useful signals. This affects both audit readiness and incident response, because teams cannot quickly answer basic questions like what exists, who has access, where data moves, and which alerts actually matter.
A practical way to reduce this risk is unified monitoring and consolidated reporting. Centralized visibility across cloud accounts, regions, and services helps teams detect drift earlier and produce consistent evidence when audits arrive.
A cloud security service provider can take this work off your plate by giving you a clear, unified view across accounts and cloud vendors. We know how to turn that visibility into action: tighten identity and access, set secure baselines, configure logging and alerting, and continuously check for drift and risky changes.
You also get practical compliance support, like mapping controls to your framework, keeping evidence organized, and preparing for audits without last-minute chaos. Your team can focus on shipping while we keep your cloud secure and audit-ready.
Penetration testing of a cloud-native hospital management system before the annual ISO 27001 audit
Final Thoughts
Cloud security compliance is daily operational work. It means defining control ownership, enforcing it across providers, and keeping evidence current. As organizations expand their cloud computing environments, they need a practical approach to ensuring cloud compliance across identities, configurations, and cloud resources.
Several shifts are shaping programs now. First, continuous compliance monitoring is moving from aspiration to expectation. Without close coordination between compliance and security teams, gaps appear between written policy and live controls, which increases compliance challenges, weakens risk management, and raises the chance of security incidents.
Second, data sovereignty is influencing architecture decisions. Gartner forecasts European sovereign cloud IaaS spending to rise from $6.9B in 2025 to $12.6B in 2026, reinforcing the need for clear residency controls and regional governance. Where cloud data lives, how data storage is structured, and how data privacy requirements are enforced now play a bigger role in platform design.
That is why teams need clearer regional governance, stronger alignment with cloud compliance frameworks and other common cloud compliance frameworks, and a more disciplined process for maintaining compliance over time rather than trying to obtain cloud compliance once and treat it as finished.
This is also where cloud security testing plays a steady role. Integrated validation, configuration reviews, and controlled attack simulations help confirm that controls work as designed and stay aligned with regulatory expectations.

FAQ

The main challenges are shared responsibility, multi-cloud complexity, and constantly evolving regulations. Cloud security compliance refers to aligning legal requirements with technical controls across providers, service models, and regions.
Data residency rules, identity governance, and continuous evidence collection add further pressure. The difficulty is less about knowing the rules and more about enforcing them consistently to maintain cloud compliance and maintain security in changing environments.
No, it is not the same across all providers. While major platforms follow similar principles promoted by groups like the Cloud Security Alliance, their services, configurations, logging formats, and default settings differ.
Responsibility boundaries also shift depending on the service model. This affects your security posture, so controls must be mapped and validated per provider and workload, not assumed to be identical everywhere.
Cloud compliance refers to identifying where sensitive data is stored, processed, and transferred. Then apply strong security measures such as data encryption, access control, logging, and retention policies to protect sensitive data and reduce the risk of data breaches.
Use structured approaches like information security management systems to support compliance and data protection. Regular cloud security and assessments help confirm that safeguards match policies and that evidence is ready if regulators request it.

















 TechMagic Academy
TechMagic Academy








